How to Enable BitLocker Hardware Encryption with SSDs
- Windows Internals
- Published Jan 7, 2015 Updated Oct 2, 2019
2019-10-01: with the 2019 September update KB4516045 BitLocker uses software instead of hardware encryption by default. Likely reason: the security of software encryption can be controlled by Microsoft. Hardware encryption in the drive may be buggy.
Beginning with Windows 8 BitLocker can offload the encryption from the CPU to the disk drive. But enabling that can be challenging. Here is how.
Why Use Hardware Encryption?
Doing encryption in hardware on the disk drive instead of in software by the CPU should be more effective. That translates into longer battery life and higher performance. AnandTech has some numbers that illustrate these points.
Requirements
These are the system requirements according to TechNet:
For data drives:
- The drive must be in an uninitialized state.
- The drive must be in a security inactive state.
If the drive is used as a startup drive the following apply additionally:
- The computer must always boot natively from UEFI.
- The computer must have the Compatibility Support Module (CSM) disabled in UEFI.
- The computer must be UEFI 2.3.1 based and have the EFI_STORAGE_SECURITY_COMMAND_PROTOCOL defined.
One very important thing is uninitialized state: it means that you cannot clone a drive with data on it and enable BitLocker with hardware encryption afterwards.
Problem: Intel Rapid Storage Technology Driver
What Microsoft does not list in their requirements is that older versions of the Intel Rapid Storage Technology Driver prevent hardware encryption. There is a 12-page thread in the Lenovo forums mainly about this problem. Version 13.2 of the RST driver fixes the issue, so make sure you have at least that version installed.
I would not recommend the alternative solution of not installing the RST driver. As the German magazine c’t found out it may increase your system’s idle power consumption.
Instructions
The following instructions worked for me. I am using a Samsung SSD 850 Pro as data drive, so the UEFI requirements do not apply (although I do have the BIOS mode set to UEFI). The computer is a Lenovo W540 laptop. The main points are:
- Update your RST driver to at least version 13.2.4.1000
- Wipe the disk with diskpart clean
- Use Samsung Magician to switch the Encrypted Drive status to ready to enable
- Reboot
- Initialize and format the drive
- Enable BitLocker
The following sections explain the process in more detail.
Update the RST Driver
I had version 12.8.10.1005 of the RST driver installed and Windows Update would not offer any newer version. A visit to Intel’s Download Center got me 13.2.4.1000.
Before the update Samsung Magician would give me the error Failed to perform the operation on the selected disk and all data security modes would be disabled. After the update that was gone.
Diskpart Clean
The disk needs to be in uninitialized state. Open an elevated command prompt and type (this deletes all data on your second hard disk!):
- diskpart
- list disk
- select disk 1
- clean
Samsung Magician
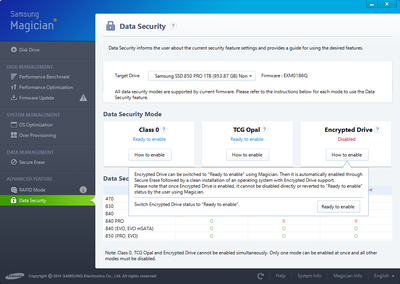
Enable Encrypted Drive status in Samsung’s SSD management software by clicking Ready to enable:
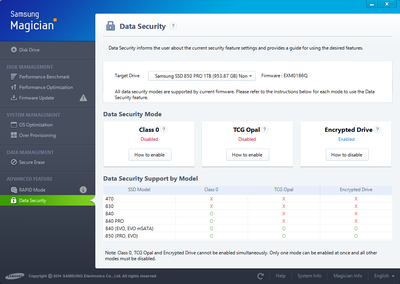
After a reboot it should look like this:
Format the Drive
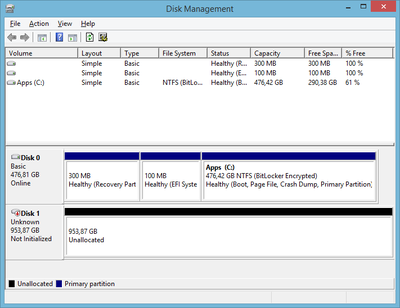
Initialize and format the drive in Disk Management. Remember: before you do that the drive should be in uninitialized state like this:
Enable BitLocker
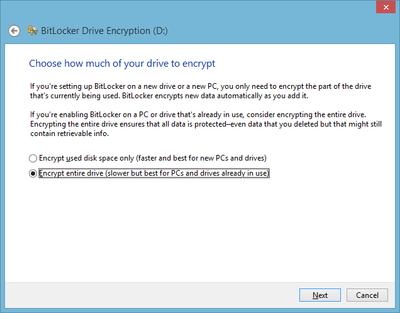
Enable BitLocker the usual way. Make sure you do not get the following screen asking how much of the drive to encrypt, otherwise BitLocker is encrypting in software:
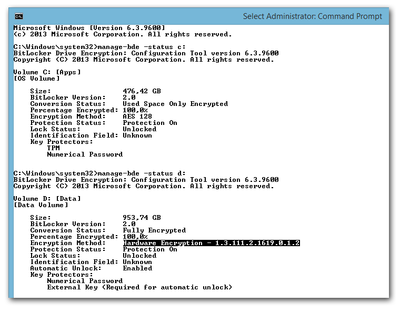
Check if BitLocker really uses Hardware Encryption
The BitLocker UI in Control Panel does not tell you whether hardware encryption is used, but the command line tool manage-bde.exe does when invoked with the parameter status. You can see that hardware encryption is enabled for D: (Samsung SSD 850 Pro) but not for C: (Samsung SSD 840 Pro without support for hardware encryption):







Comments