Do You Still Hide Your Share$?
- Security
- Published Mar 1, 2009 Updated Jun 22, 2021
Fighting Another Legacy of the NT Era
Hiding network shares by appending a dollar sign is a common practice among administrators. While by itself that is neither good nor bad, it is a perfect example of how customs establish themselves in the IT industry in exactly the same way they do in other subcultures. Putting it differently, another fine specimen of an IT legend.
Although I would very much like to, I cannot provide a history of how and when the dollar share custom got established. What I can say is that when I started my IT career in the late 90s, the custom was already prevalent. “Good” administrators hid their shares, whilst “bad” or careless admins did not. It has been a source of pride for many an administrator (including myself for a long time) to have an “invisible” network. The benefits? Apart from feeling good about running a tight ship, security (apparently) is guaranteed and end-users do not get confused by the myriad of shares.
Security…
Do you still think dollar shares are hidden? I myself did until recently when a colleague mentioned that I was very much mistaken, indeed. At first, I would not believe him, but I soon realized that filtering of shares is not done at the (file) server, but at the client.
What? The client?!!
If there is one golden rule in security, it is this: “Never trust the client”. Sending information to the client it is not supposed to see is a no-go.
But then, not everybody adheres to this simple principle. Or knows about it. The dollar share issue probably dates back to the LAN Manager days, when security was associated with bodyguards, not IT systems.
…by Obscurity
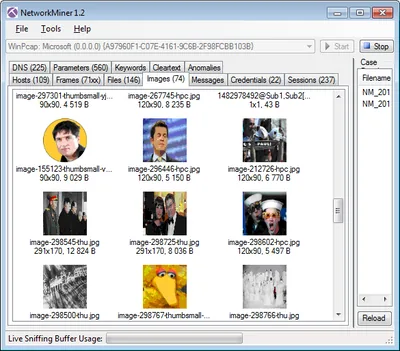
One way or another, the problem with dollar shares is this: the server always sends a full list of its shares to any client asking for them. It lies in the “responsibility” of the client to filter out the dollar shares. Such a methodology obviously cannot last forever: There are tools out there in the wild, wild net that disrespectfully ignore the etiquette and display all shares returned by the server. One of the more respectable of such tools is by now owned by Microsoft itself, Sysinternals ShareEnum. Another one is even built into the operating system starting with Vista: net view \\computername /all.
Moving on
Using dollar shares obviously is superfluous. It adds a layer of security that is only felt by the administrator but really does not exist.
One open question remains: How to hide unnecessary folders from end users. The answer is simple: Use DFS in conjunction with access-based enumeration (ABE).




Comments