Removing “Eject VMware Virtual disk SCSI Disk Device”
The HotPlug functionality of VMware ESX(i) 4 and 5 has the negative side effect that it is easily possible to “eject” hardware devices from inside the virtual machine, completely removing the respective device from the VM configuration. This is especially bad if it happens to the network card, and others have already described how to prevent that from happening (e.g. here and here).
Ejectable Disk Device
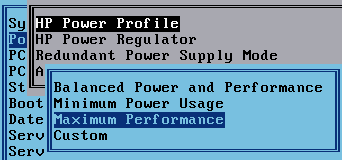
One thing remains, even when disabling HotPlug by adding the following line to the virtual machine’s properties as recommended by VMware:
devices.hotplug = "false"
The Safely Remove Hardware icon is still shown in the taskbar. If clicked, a popup windows opens with the command Eject VMware Virtual disk SCSI Disk Device as can be seen in this (German) screenshot:

Ejecting a virtual machine’s only disk is a very bad idea, of course, and luckily it does not work because the device is in use. But concluding that all is well is not suffienct if user experience is at all relevant. Simply hiding the Safely Remove Hardware icon through Group Policy is also not an option if the users connect USB devices via XenDesktop’s USB redirection mechanism – because in that case they need the icon.
Making an Ejectable Device Un-Ejectable
The way to get rid of the option to eject the virtual disk is to make Windows believe that it is not hot-pluggable. This can be achieved by modifying the corresponding device capabilities registry value. That, however, is complicated by the facts that only SYSTEM has write access to the registry key and that Windows re-writes the correct value when booting – re-enabling HotPlug. The solution is to execute a computer startup script via Group Policy. Startup scripts are run in SYSTEM context, and since the script runs every time the system is booted we can be sure the device capabilities value is always configured the way we want it to be.
To implement the solution, create a batch file with the following content and run it as a computer startup script:
:: Disable eject hard disk
:: Original value: 6
reg.exe add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Enum\PCI\VEN_1000&DEV_0054&SUBSYS_197615AD&REV_01\4&1f16fef7&0&00A8" /v Capabilities /t REG_DWORD /d 2 /f
:: Disable eject network card
:: Original value: 6
reg.exe add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Enum\PCI\VEN_8086&DEV_100F&SUBSYS_075015AD&REV_01\4&3ad87e0a&0&0088" /v Capabilities /t REG_DWORD /d 2 /f
Note: The second command is for disabling network card ejection. This is an alternative to setting “devices.hotplug=false” in the VMX file.
How Does it Work?
During the boot phase Windows probes the hardware and writes each device’s capabilities to the Capabilities registry value. According to this answer on superuser.com, bit no. 3 equals CM_DEVCAP_REMOVABLE:
//from inc/api/cfgmgr32.h (WINDDK)
#define CM_DEVCAP_LOCKSUPPORTED (0x00000001)
#define CM_DEVCAP_EJECTSUPPORTED (0x00000002)
#define CM_DEVCAP_REMOVABLE (0x00000004)
#define CM_DEVCAP_DOCKDEVICE (0x00000008)
#define CM_DEVCAP_UNIQUEID (0x00000010)
#define CM_DEVCAP_SILENTINSTALL (0x00000020)
#define CM_DEVCAP_RAWDEVICEOK (0x00000040)
#define CM_DEVCAP_SURPRISEREMOVALOK (0x00000080)
#define CM_DEVCAP_HARDWAREDISABLED (0x00000100)
#define CM_DEVCAP_NONDYNAMIC (0x00000200)
All we have to do is make sure the bit is not set. We do that by changing the Capabilities registry value from 6 (bits 2 + 3 set) to 2 (only bit 2 set).




14 Comments
Hi Helge!
Thanks for this post! This information was very useful for me because it was becoming a problem in my VDI environment.
But.. for me, using only devices.hotplug = “false” was sufficient. It has hid both NIC e SCSI devices eject capabilities.
In time, my versions are:
ESXi – 5.0.0 (build 504890)
vCenter – 5.0.0 (build 623373)
Virtual Hardware Version – 8
SO – Windows 7 Pro 32 bit
Adding “devices.hotplug = “false”” works for me too, without the additional startup script.
ESXi – 5.0.0 (build 768111)
vCenter – 5.0.0 (build 755629)
Virtual Hardware Version – 8
OS – Windows Server 2008 R2
this works great for win7 desktops deliver a registry key via GPO….but it does not work for XP desktops, it there a fix for XP as well?
Can also be done with a Powershell Computer Startup script:
# Script to remove Eject property on VMware NICs (based on http://tsmith.co/2011/vm%E2%80%99s-nic-shows-as-a-removable-device/)
# The keys are reverted after reboot so needs to be run as a startup script under SYSTEM credentials to be able to change the value
#
# 12-jul-2013 Bart Hoofd Initial script
# List of VMware NIC device IDs and name (paired as (“DeviceID”,”Name”), name is for documentation and optional logging only)
$VMNICDeviceIDs = ,((“VEN_15AD&DEV_07B0&SUBSYS_07B015AD&REV_01″,”vmxnet3 Ethernet Adapter”))
# Enumerate all devices in the list
ForEach ($VNDI in $VMNICDeviceIDs)
{
If ($VNDI[0] -ne $NULL)
{
# Retrieve the proper registry key and check if it exists
$DevKey = “Registry::HKLM\SYSTEM\CurrentControlSet\Enum\PCI\”+$VNDI[0]
If ((Test-Path $DevKey) -eq $True)
{
# Get the local system subkey for this device ID
$VMNICs = Get-ChildItem $DevKey
ForEach ($VMNIC in $VMNICs)
{
If ($VMNIC -ne $NULL)
{
# Check the Capabilities value, subtract 0x4 from it and set (this bit enabled Eject: CM_DEVCAP_REMOVABLE (0x00000004))
$CapVal = (Get-ItemProperty $VMNIC.PSPath -Name Capabilities).Capabilities
If (($CapVal -band 0x4) -eq 0x4)
{
$NewCapVal = $CapVal -bxor 0x4
$OK = Set-ItemProperty $VMNIC.PSPath -Name Capabilities -Value $NewCapVal
}
}
}
}
}
}
Thanks, Bart! This is just what I’m looking for…
I copied and pasted the above script in ISE, but it’s full of errors from the way the comment system applied your post. I followed the blog link you posted but it’s missing.
Do you have this scrip somewhere else I can get to it?
Thanks!
EB
What can I do, when the vmxnet3 nic has named “vmxnet3 Ethernet Adapter #2”? In ps scripts you can’t use a pound within a command.
Thanks in advance
Excellent script Bart :-) !
The script doesnt work, i had to change 0*4 to 0*16but still see ethernet to remove
Concerning the NIC your registry keys seem to address E1000 nic’s if you (like me) are using vmxnet3 adapters you’ll have to change the 2nd registry key to
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Enum\PCI\VEN_15AD&DEV_07B0&SUBSYS_07B015AD&REV_01\FF565000DB4483FE00
Still very useful! :-)
Any idea how to get this working in Windows 10? Works in my Win7…but not Win10. Seems that the Capabilities value is different.
Doesn’t work for the network cards as VMX Net Entries are wrong HKEY path
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Enum\PCI\VEN_1000&DEV_0054&SUBSYS_197615AD&REV_01\4&2509f6e&0&00A8 for primary
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Enum\PCI\VEN_15AD&DEV_07B0&SUBSYS_07B015AD&REV_01\FF565000B210B8FE00 for secondary on mine
Capabilities also very different I have 0x16 on mine as original. So not sure which value to use for this even if you use the correct HKEY
This article is from 2012 and later updated in 2013… I guess something has changed in the past 10+ years :)