Locking Down Internet Explorer 8 with Group Policy
Managing Internet Explorer via group policy is a daunting task. Hundreds of policies are available to control the browser’s user interface, security settings and much more. This article lists strategies and scripts I have found helpful.
ActiveX Controls and Add-Ons
There are two different ways to control the execution of ActiveX controls: either by enabling administrator approval mode for a specific zone, typically the internet zone, and adding the CLSIDs of allowed controls via custom ADM templates. Or globally via the add-on management, where CLSIDs can be specified without authoring custom ADM templates. In this article I describe the second method.
It basically works like this: Allow the execution of ActiveX controls in the internet zone. Do not configure administrator approval mode. Then deny all add-ons except those whose CLSIDs have been added to a list.
We need a way to configure which controls we want to run. We do this in the policy category Windows Components\Internet Explorer\Security Features\Add-on Management. Enable “Deny all add-ons unless specifically allowed in the Add-on List”, then add the CLSIDs of all allowed add-ons to the “Add-on List”.
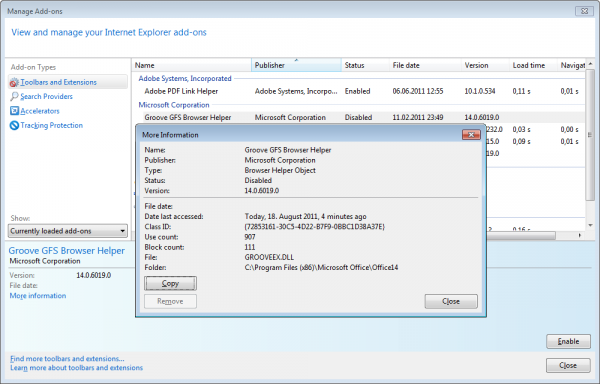
Finding a component’s CLSID sometimes is simple with IE8. Surf to a site where one or more add-ons are blocked. Open the add-on management dialog (in the tools menu or from the browser’s status bar). You will notice that at least one add-on is in disabled state. Double-click the disabled add-on to open a dialog with additional information, including the add-on’s CLSID:
Click “Copy” to copy the add-on’s CLSID to the clipboard and paste it into the “Add-on List” policy with a value of 1 (allow).
Repeat this process for all add-ons you want to allow.
There are situations in which above procedure does not work because the add-on is not statically referenced but dynamically instantiated from code (JavaScript). In such cases the script typically fails and IE displays a yellow warning icon in the status bar. Double-clicking that gives you a dialog with some information, including the full URL to the script file and the line number where it failed. Copy the URL and download the script. Open it in a text editor, go to the line where the error occured and you may find something like this:
function WDSAjax () {
this.callBackMethod = "";
if (navigator.appName == "Microsoft Internet Explorer") {
WDSAjaxRequestObject = new ActiveXObject("Microsoft.XMLHTTP");
} else {
WDSAjaxRequestObject = new XMLHttpRequest();
}
}
In this example from the Lufthansa website the error is caused by the script trying to instantiate a new Microsoft.XMLHTTP ActiveX control and not checking whether that actually succeeded. It failed, of course, because the control’s CLSID is not in the list of allowed add-ons. To find the CLSID open regedit and navigate to HKEY_CLASSES_ROOT\Microsoft.XMLHTTP\CLSID, copy the default value’s data ({ED8C108E-4349-11D2-91A4-00C04F7969E8} in this example) and add it to the add-on list.
For other examples please see the chapters about the Citrix Online Plugin and about the script GetBlockedIEAddons.vbs below.
Citrix Web Interface and Online Plugin (ICA Client)
If you use the policy setting “Deny all add-ons unless specifically allowed in the Add-on List” you may find that launching published applications from the web interface does not work. Instead of connecting to XenApp the browser seems to download something (blue progress bar shows up quickly) but then nothing happens. Instead you are informed that some add-ons have been blocked. But which ones?
In addition to the obvious Citrix.ICAClient (CLSID {238F6F83-B8B4-11CF-8771-00A024541EE3}) you need to enable the “Microsoft Web Browser” control Shell.Explorer with the CLSID {8856F961-340A-11D0-A96B-00C04FD705A2}.
How did I find that out? As so often, Sysinsternals Process Monitor proves to be an invaluable debugging tool. I used it as follows:
- Start IE and log on to the Citrix Web Interface. You probably already see the blocked add-on icon in the status bar.
- Start Process Monitor. Set a filter to only include events from IExpore.exe. Clear the log and start the trace.
- In IE click the icon of a published application / desktop which then fails to launch.
- In Process Monitor stop the trace and look for GUIDs. In this case, the last GUID I found in the trace was the one of the missing component.
- Add the GUID you found to the list of allowed add-ons and test.
Google Maps
Enable these settings for Google Maps to work correctly:
- Active scripting
- Binary and script behaviors
- Run ActiveX controls and plug-ins
Script GetBlockedIEAddons.vbs
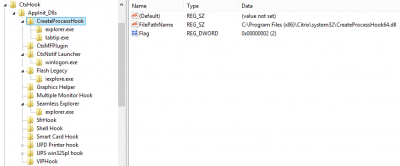
You might have gotten the impression that finding blocked add-ons is a difficult task, and it is. But here is an abbreviation that often works: Internet Explorer logs the CLSIDs of blocked add-ons by creating entries in the registry below HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats. Below the Stats key are subkeys named like CLSIDs. If a CLSID has been blocked, IE adds a value “Blocked” like this:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{18DF081C-E8AD-4283-A596-FA578C2EBDC3}\iexplore\Blocked=4 [DWORD]
Sifting through the registry looking for “Blocked” values is certainly possible, but time-consuming. A script can do that much more efficiently. Here is the code for GetBlockedIEAddons.vbs, a script that lists blocked add-ons for any user on the local or a remote computer. Remember to adjust the variables computerName and userSID.
'
' GetBlockedIEAddons.vbs by Helge Klein
'
' Determines which Add-ons for Internet Explorer have been blocked
' for a specific user on a specific computer.
'
' Based on a script by Alan Evans (http://forums.citrix.com/message.jspa?messageID=1445696)
'
'
' Variables - adjust to your needs
'
' Dot (.) for local computer
computerName="."
' SID of user account to search
userSID="S-1-5-21-789336058-920026266-854245398-3701"
' Path and name of output file
outFile="Blocked Addon Report.txt"
'
' Constants
'
Const HKEY_LOCAL_MACHINE = &H80000002
Const HKEY_USERS = &H80000003
'
' Start of script
'
' Open the remote registry
Set oReg=GetObject("winmgmts:{impersonationLevel=impersonate}!\\" & computerName & "\root\default:StdRegProv")
' Get the CLSID subkeys
strKeyPath = userSID & "\Software\Microsoft\Windows\CurrentVersion\Ext\Stats"
oReg.EnumKey HKEY_USERS, strKeyPath, arrSubKeys
' Get information for each blocked CLSID subkey
For Each subkey In arrSubKeys
oReg.GetDWORDValue HKEY_USERS,strKeyPath & "\" & subkey & "\iexplore","Blocked",dwValue
if dwvalue <> "" Then
StrMsg = StrMsg & "Blocked CLSID : " & subkey & vbcr & vblf
oReg.GetStringValue HKEY_LOCAL_MACHINE,"Software\Classes\CLSID\" & Subkey & "\ProgID","",strValue
StrMsg = StrMsg & " ProgID : " & StrValue & vbcr & vblf
oReg.GetStringValue HKEY_LOCAL_MACHINE,"Software\Classes\CLSID\" & Subkey & "\InprocServer32","",strValue
StrMsg = StrMsg & " Executable : " & StrValue & vbcr & vblf
end if
Next
' Write the report to a file...
Set fso = CreateObject("Scripting.FileSystemObject")
Set oFile = fso.OpenTextFile(outFile, 2, True)
oFile.WriteLine StrMsg
oFile.Close
' ...and show it to the user
msgbox StrMsg,4096,"Blocked Addon Report"
Search Providers
By default Internet Explorer searches with Bing, obviously. Adding additional search providers is possible by adding keys below “Software\Policies\Microsoft\Internet Explorer\SearchScopes” via a custom group policy ADM template, for example. Setting the default search provider should be possible by setting the value DefaultScope to the key name of the search provider. In case of Google, that would look like this:
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\SearchScopes\DefaultScope={66D6A6DF-F354-4C9A-AFB9-56F5950A5E85}
Unfortunately, this does not work in IE8 (but in IE7 and IE9). IE8 always uses the search provider as default whose key is first in alphabetical order! To set Google as default and add Wikipedia, too, you could use the following registry snippet:
Windows Registry Editor Version 5.00
[HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\SearchScopes]
"DefaultScope"="1-Google"
[HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\SearchScopes\1-Google]
"DisplayName"="Google"
"URL"="http://www.google.com/search?q={searchTerms}&rls=com.microsoft:{language}&ie={inputEncoding}&oe={outputEncoding}&startIndex={startIndex?}&startPage={startPage}"
"ShowSearchSuggestions"=dword:00000001
"SuggestionsURL_JSON"="http://suggestqueries.google.com/complete/search?output=firefox&client=IE8&qu={searchTerms}"
"SuggestionsURL"="http://clients5.google.com/complete/search?hl={language}&q={searchTerms}&client=ie8&inputencoding={inputEncoding}&outputencoding={outputEncoding}"
"OSDFileURL"="http://download.microsoft.com/download/A/3/C/A3C89D63-E2F0-460D-9F5F-23B51EA52B5E/Google.xml"
"FaviconURL"="http://www.google.com/favicon.ico"
"FaviconPath"="C:\\Users\\hklein.SEPAGO\\AppData\\LocalLow\\Microsoft\\Internet Explorer\\Services\\search_{66D6A6DF-F354-4C9A-AFB9-56F5950A5E85}.ico"
[HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\SearchScopes\2-Bing]
"SuggestionsURLFallback"="http://api.bing.com/qsml.aspx?query={searchTerms}&maxwidth={ie:maxWidth}&rowheight={ie:rowHeight}§ionHeight={ie:sectionHeight}&FORM=IE8SSC&market={language}"
"FaviconURLFallback"="http://www.bing.com/favicon.ico"
"DisplayName"="Bing"
"URL"="http://www.bing.com/search?q={searchTerms}&src=IE-SearchBox&FORM=IE8SRC"
"TopResultURLFallback"="http://www.bing.com/search?q={searchTerms}&src=ie9tr"
[HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\SearchScopes\3-Wikipedia]
"DisplayName"="Wikipedia (en)"
"URL"="http://en.wikipedia.org/wiki/Special:Search?search={searchTerms}"
"ShowSearchSuggestions"=dword:00000001
"SuggestionsURL"="http://en.wikipedia.org/w/api.php?action=opensearch&format=xml&search={searchTerms}&namespace=0"
"OSDFileURL"="http://download.microsoft.com/download/8/c/f/8cf73e43-b5ba-416c-8596-2535416e3be0/Wikipedia.xml"
"FaviconURL"="http://en.wikipedia.org/favicon.ico"
Note: As mentioned setting the default search provider via the value DefaultScope does not work in IE8. It is included here for completeness sake and for use with IE7 and IE9.
Notes
All policy settings mentioned here can be set per user.
References
Group Policy and Internet Explorer 8 on TechNet





1 Comment
This is very helpful, thank you.