How to Find and List Unsigned Executable Files
Executable files can (and should be!) digitally signed. Without a digital signature you can never be sure the files on your hard disk have not been tampered with. There is really no exception to this rule, except maybe smaller open source projects that lack the budget to buy the digital certificate required for signing. Digitally signing executable files is so important that Microsoft made it a requirement in the Windows 7 Logo Program. One might think that such a simple yet important thing as signed executables can be taken for granted by now. Well, let’s have a look!
Finding the Black Sheep
I have written a simple batch script that scans a given directory tree for files of a certain type and checks each matching file for a valid digital signature. The script can be downloaded, but here it is in all its beauty:
@echo off
::
:: Author: Helge Klein
::
:: Prints out a list of all unsigned files (NOT digitally signed) whose names match a given pattern.
:: Recursively searches a folder structure beginning at a given base directory.
::
:: Prerequisites:
::
:: - Signtool.exe is used to check the Authenticode signature of executable files.
:: It must be found in the path.
:: Signtool is part of the .NET Framework SDK. Information: http://msdn.microsoft.com/en-us/library/aa387764.aspx
::
::
:: Variables
::
:: Base directory
set SEARCH_BASE="C:\Program Files (x86)"
:: Files to be checked (wildcards allowed). Examples: *.exe or *.dll or *.sys
set FILTER=*.DLL
::
:: Start of script
::
for /f "usebackq tokens=*" %%i in (`^dir /s /b %SEARCH_BASE%\%FILTER%`) do (call :CheckSignature "%%i")
goto :eof
:CheckSignature
signtool.exe verify /pa /q "%~1" 1>nul 2>nul
if errorlevel 1 echo %~1
goto :eof
Results
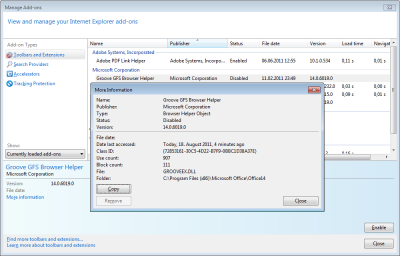
On the machine I am writing this, the script found 702 unsigned DLLs in the 32-bit program files folder alone. 702!! And most of them not by some open source project but by Microsoft, Citrix, VMWare, Adobe, Sun (Java)… Of course, I have the latest versions installed, so the lack of signatures is not due to me using dated software written in the stone age of computing.
What does my spot check tell us? Security does not seem to be taken seriously enough even by the largest software manufacturers. But unless every executable file is signed, policies blocking unsigned files cannot be put into effect. It looks like it might take some more years before digital signatures can be a truly powerful tool.
Notes
The following file types are considered executable files in the Windows 7 Logo Technical Requirements document: EXE, DLL, OCX, SYS, CPL, DRV, SCR. The document states that all executables must be signed with an Authenticode certificate, but leaves a loophole:
“Waivers will be considered only for unsigned third-party redistributables. A proof of communication to request a signed version of the redistributable(s) is required for this waiver to be granted.“



1 Comment
If you need this without the recursiveness, simply removing the /s won’t work, since without it, dir won’t include the full path in %%i.
Instead, you can replace (`^dir /s /b %SEARCH_BASE%\%FILTER%`) to (`^where %SEARCH_BASE%:%FILTER%`)
This works at least on Windows 10. Note that the ” \ ” was changed to ” : ” between %SEARCH_BASE% and %FILTER%.