Windows 7 Default HKCU Registry Permissions
- Permissions
- Published Sep 4, 2012
This is a complete listing of all Windows 7 HKEY_CURRENT_USER registry permissions. The list was generated on a 32-bit installation with SetACL. More default permission listings can be found here.
How to Interpret the List
As mentioned above the list contains only non-inherited permissions. This means that if permission X is set on HKCU and the subkey HKCU\Software is configured to not block inherited permissions, X is valid on HKCU\Software, too. The permissions of HKCU\Software will not be included in this listing, because that would make it much, much longer and harder to read.
If a key is configured to not inherit permissions from its parent it is marked with “DACL(protected)” or “DACL(pseudo_protected)”. A key that does inherit from its parent can still add permissions not present in the parent. Those are listed here, of course.
Remarks
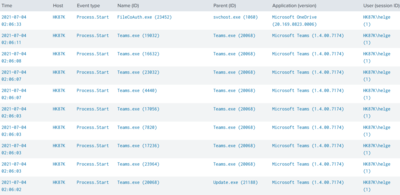
The computer where I created this listing was a domain member and had a local user account named “Helge”.
Permission Listing
HKCU
Owner: BUILTIN\Administrators
DACL(protected):
HK\helge full allow container_inherit+object_inherit
NT AUTHORITY\SYSTEM full allow container_inherit+object_inherit
BUILTIN\Administrators full allow container_inherit+object_inherit
NT AUTHORITY\RESTRICTED read allow container_inherit+object_inherit
HKCU\Software\Microsoft\EventSystem
Owner: NT AUTHORITY\SYSTEM
DACL(protected+auto_inherited):
BUILTIN\Administrators full allow container_inherit
CREATOR OWNER full allow container_inherit+inherit_only
HK\helge full allow container_inherit
NT AUTHORITY\SYSTEM full allow container_inherit
NT SERVICE\EventSystem read allow container_inherit
HKCU\Software\Microsoft\Internet Explorer\User Preferences
Owner: HK\helge
DACL(not_protected+auto_inherited):
HK\helge KEY_SET_VALUE+KEY_WRITE deny no_inheritance
HKCU\Software\Microsoft\Protected Storage System Provider\<SID>
Owner: BUILTIN\Administrators
DACL(pseudo_protected):
NT AUTHORITY\SYSTEM full allow container_inherit
HKCU\Software\Microsoft\SystemCertificates\Root\ProtectedRoots
Owner: HK\helge
DACL(pseudo_protected):
NT SERVICE\CryptSvc full allow container_inherit
HK\helge read allow container_inherit
HKCU\Software\Microsoft\Windows\CurrentVersion\Group Policy
Owner: NT AUTHORITY\SYSTEM
DACL(pseudo_protected):
NT AUTHORITY\SYSTEM full allow no_inheritance
BUILTIN\Administrators full allow no_inheritance
HK\helge read allow no_inheritance
HK\helge read allow container_inherit+object_inherit+inherit_only
NT AUTHORITY\SYSTEM full allow container_inherit+object_inherit+inherit_only
BUILTIN\Administrators full allow container_inherit+object_inherit+inherit_only
HKCU\Software\Microsoft\Windows\CurrentVersion\Policies
Owner: NT AUTHORITY\SYSTEM
DACL(protected):
NT AUTHORITY\SYSTEM full allow container_inherit+object_inherit
BUILTIN\Administrators full allow container_inherit+object_inherit
NT AUTHORITY\RESTRICTED read allow container_inherit+object_inherit
HK\helge read allow container_inherit+object_inherit
HKCU\Software\Policies
Owner: NT AUTHORITY\SYSTEM
DACL(protected):
NT AUTHORITY\SYSTEM full allow container_inherit+object_inherit
BUILTIN\Administrators full allow container_inherit+object_inherit
NT AUTHORITY\RESTRICTED read allow container_inherit+object_inherit
HK\helge read allow container_inherit+object_inherit
HKCU\Software\Classes
Owner: NT AUTHORITY\SYSTEM
DACL(protected):
HK\helge full allow container_inherit+object_inherit
NT AUTHORITY\SYSTEM full allow container_inherit+object_inherit
BUILTIN\Administrators full allow container_inherit+object_inherit
NT AUTHORITY\RESTRICTED read allow container_inherit+object_inherit
HKCU\Software\Classes\VirtualStore
Owner: NT AUTHORITY\SYSTEM
DACL(protected):
HK\helge full allow container_inherit+object_inherit
NT AUTHORITY\SYSTEM full allow container_inherit+object_inherit
BUILTIN\Administrators full allow container_inherit+object_inherit
NT AUTHORITY\RESTRICTED read allow container_inherit+object_inherit
HKCU\Software\Classes\VirtualStore\MACHINE
Owner: NT AUTHORITY\SYSTEM
DACL(protected):
HK\helge full allow container_inherit+object_inherit
NT AUTHORITY\SYSTEM full allow container_inherit+object_inherit
BUILTIN\Administrators full allow container_inherit+object_inherit
NT AUTHORITY\RESTRICTED read allow container_inherit+object_inherit
HKCU\System\CurrentControlSet\Policies
Owner: NT AUTHORITY\SYSTEM
DACL(protected):
NT AUTHORITY\SYSTEM full allow container_inherit+object_inherit
BUILTIN\Administrators full allow container_inherit+object_inherit
NT AUTHORITY\RESTRICTED read allow container_inherit+object_inherit
HK\helge read allow container_inherit+object_inherit




Comments