Remote Management of Windows PCs in an Isolated Security Zone
- Security
- Published Jan 15, 2014
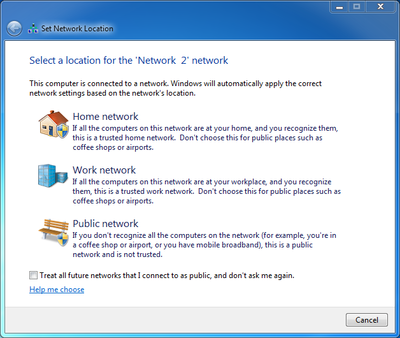
With the advent of BYO it has become fashionable to regard PCs as untrusted devices that should be isolated in a dedicated security zone.
Zoning
Such an approach has a big advantage: by separating clients from servers it is possible to treat them differently and potentially apply more relaxed security policies - which is a basic requirement for BYO. In a truly BYO-only environment you block everything except Citrix ICA or some other remoting procotol of choice at the firewall and life is good. In real corporate networks things are a bit more complicated, however. Say you want to isolate your managed Windows PCs. In that case you might want to be able to manage them remotely from systems outside the client security zone (e.g. from management terminal servers). And suddenly you have a problem: Windows management protocols, especially RPC and DCOM, are not exactly firewall-friendly.
 by [Mick Baker](http://www.flickr.com/photos/36593372@N04/) under [CC](http://creativecommons.org/licenses/by-nd/2.0/) Business Zone by Mick Baker under CC](/images/2014/01/generated/Business-Zone_400w.1b7b399d480274a5131b087fdc7faec8a6bf74b762eb2462f65e6a8e892e32fc.webp)
RPC
By default, RPC and DCOM use a dynamic port range that spans ports 49152 through 65535. That is a big range and the firewall guys will not be happy opening it up. They will ask you to specify individual ports instead of an entire range. Unfortunately the nature of the RPC protocol makes it impossible to channel all communications through a single port. While it is possible to restrict the RPC ports to a smaller range, such a modification constitutes a major change (difficult in production) and may break applications if the chosen range is too small.
Remote Management without RPC
RPC is a legacy protocol. Might it be possible to simply ignore it and not open the firewall for RPC? Modern tools use HTTP(S) while many of the older tools might work without RPC, too.
I tested that assumption in a configuration where Windows 7 PCs were behind a firewall configured to allow the following management traffic:
- 135 TCP (RPC)
- 137 UDP (RPC)
- 138 UDP (NetBIOS)
- 139 TCP (NetBIOS)
- 445 TCP (SMB)
- 5985 TCP (WS-Man, PowerShell)
Ports 49152 through 65535 TCP+UDP (DCOM, RPC) were explicitly not opened. Then I tried various management tools from a Server 2008 R2 machine located outside the client zone with the following results:
| Management tool | Works? | Remarks |
|---|---|---|
| Event Viewer | no | Error message: The RPC server is unavailable |
| Services | yes | Establishing a new connection takes approx. 24 s |
| Regedit | yes | |
| File shares | yes | |
| Task Scheduler | no | No error message |
| Sysinternals PSExec | yes | Establishing a new connection takes approx. 24 s |
| WS-Man (CIM cmdlets) | yes |
Conclusion
This does not look too bad. Depending on your requirements remote management without RPC/DCOM might be a viable alternative to either one of the extremes “no isolation at all” and “RDP-only”.
What do you think? Did I miss important remote management tools? Let me know!






Comments