What DNS Pointer Records and Tweetups Have in Common
- Networking, UberAgent
- Published Jun 12, 2014 Updated Feb 23, 2021
Tools that monitor network traffic typically work with IP addresses, not server names. Humans, on the other hand, seem to prefer names over cryptic numbers. Most tools deal with that by doing reverse lookups of the IP addresses, i.e. they are looking for DNS PTR records. The result of such a lookup, however, is not always what you expect. Let us look at a simple example:
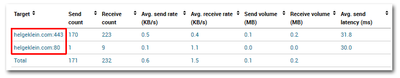
When I open my website https://helgeklein.com in Chrome that looks in Sysinternals Process Explorer like this:

Why does Process Explorer display 89-145-92-216.static.directrouter.co.uk instead of helgeklein.com? Because that is what is stored in the PTR record:
d:\>ping -n 1 helgeklein.com
Pinging helgeklein.com [89.145.92.216] with 32 bytes of data:
Reply from 89.145.92.216: bytes=32 time=26ms TTL=53
d:\>nslookup 89.145.92.216
Name: 89-145-92-216.static.directrouter.co.uk
Address: 89.145.92.216
uberAgent does not do that. It shows you the name the end user actually typed into the browser:
Having read this far you might wonder what Tweetups, mentioned in the title, have to do with all this. The answer is simple: when you interact with people on Twitter all you see is their name and a tiny, tiny profile picture. Many do not even use a headshot but something more or less different. That is no problem … until you go to a conference, Tweetup or similar. Trying to recognize real-life people standing right in front of you from the tiny Twitter profile pictures is next to impossible. Trust me - I have tried and failed too many times. And that is where this relates to name resolution: the pattern recognition system we humans are equipped with works well enough, but in no way can we cope with names like 89-145-92-216.static.directrouter.co.uk which are not much more than IP addresses in disguise. Let’s use tools that take care of these things. Let’s use uberAgent!







Comments