Solved: Disabling the BitLocker Service via GPP Fails
- Permissions
- Published Apr 17, 2012 Updated Apr 16, 2012
If you want to disable the BitLocker service via Group Policy Preferences, you will find that you cannot. The service’s startup mode stays at “manual” and the following event is logged to the application event log:
Type: Warning
Source: Group Policy Services
Event ID: 4098
User: SYSTEM
Text: ... error code 0x80070005 access denied ...
Other services can be disabled without any problems.
Analysis
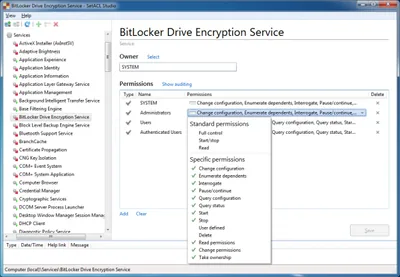
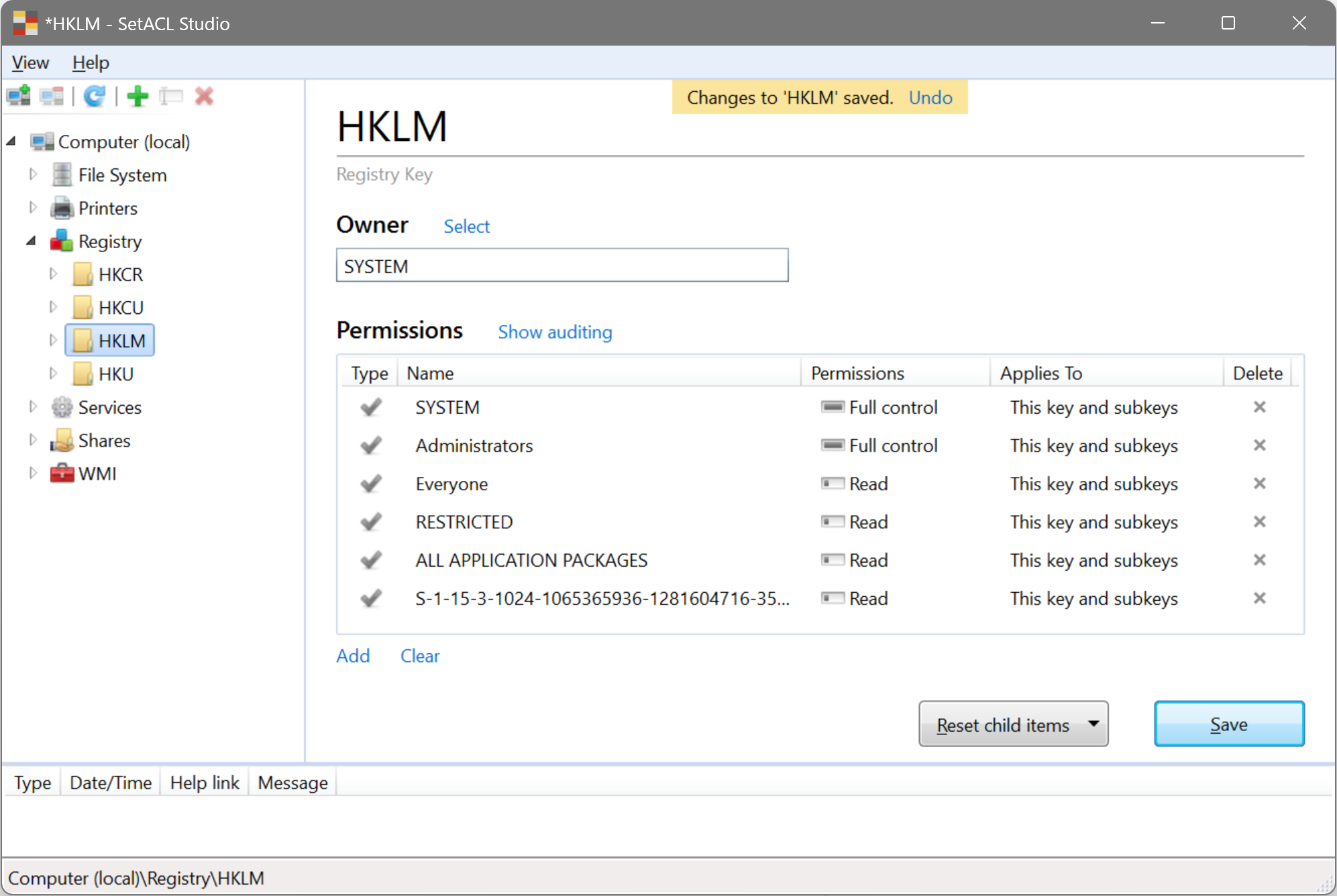
The “access denied” message points to a problem related to permissions. Looking at the BitLocker service’s permissions in SetACL Studio, we see:
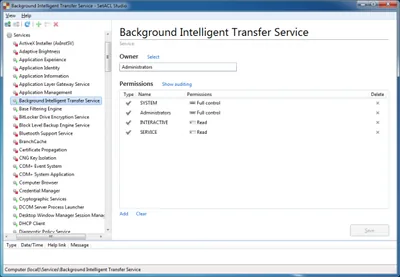
When we compare that with some other service’s permissions, we notice that other services have a much simpler permission setup, where Administrators simply have full control:
Solution
Once Administrators have full access, disabling the BitLocker service works flawlessly. Service permissions changes can be automated easily with SetACL. To grant Administrators full access to the BitLocker service use the following command:
SetACL -on BDESVC -ot srv -actn ace -ace n:Administrators;p:full




Comments